 If you are a healthcare professional you have a duty to maintain the security of patient identifiable data. Within your job you sometimes need to use a USB key to transfer lists or letters between computers. If you lose your un-encrypted USB key with patient identifiable data then it may deemed negligent and you may face disciplinary action. In this how-to I will talk through how to setup an easy to use secure software encryption scheme for a USB stick/key for use with Windows.
If you are a healthcare professional you have a duty to maintain the security of patient identifiable data. Within your job you sometimes need to use a USB key to transfer lists or letters between computers. If you lose your un-encrypted USB key with patient identifiable data then it may deemed negligent and you may face disciplinary action. In this how-to I will talk through how to setup an easy to use secure software encryption scheme for a USB stick/key for use with Windows.
The Problem
You need to take care of PID (patient identifiable data) but you don’t have the time to learn the ins and outs of encryption schemata. Even if you use your USB key to transfer the data and then delete it, if you were to lose the key and it fell into unscrupulous hands it possible that someone could read even the deleted files.
The Solution
TrueCrypt is an open source, free application that allows you to use tried-and-tested NHS approved encryption methods. It can be set up to automatically load when you plug the USB key into the PC.
How Does it work?
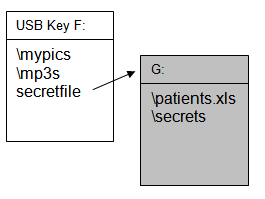 When you plug a USB stick into a PC it usually mounts the drive as a drive letter (F in this example). When TrueCrypt is running and you have entered your password you will be greeted by a second drive letter, this is the encrypted one. The files on this new drive will only be decrypted and visible to you once you have typed in your password. Existing files on your USB key will not encrypted, only ones added to the new drive letter. You have to store the encrypted files in a container I have called ‘secretfile’, but you could call it anything you wish. If someone found your USB key the encrypted data will all be enclosed safely within your file container ‘secretfile’ which someone could see exists but they would not be able to view the actual contents of the file without obtaining your password.
When you plug a USB stick into a PC it usually mounts the drive as a drive letter (F in this example). When TrueCrypt is running and you have entered your password you will be greeted by a second drive letter, this is the encrypted one. The files on this new drive will only be decrypted and visible to you once you have typed in your password. Existing files on your USB key will not encrypted, only ones added to the new drive letter. You have to store the encrypted files in a container I have called ‘secretfile’, but you could call it anything you wish. If someone found your USB key the encrypted data will all be enclosed safely within your file container ‘secretfile’ which someone could see exists but they would not be able to view the actual contents of the file without obtaining your password.
The How-to
1. Download the newest version of TrueCrypt from here.
3. Double-click on the downloaded file and it will run. You will be warned that the file has come from the internet, this is OK.
4. Accept the default terms and conditions and then select extract rather than install. You do not want to install the program on your computer as this would probably be in breach of your local IT guidelines.
5. Extract the files to your desktop, leave the box ticked that allows you to open the folder once extracted.
6. This new folder will pop-up. Plug your USB key in and note what drive it comes up as. (eg F:)
6. Run the program called “TrueCryptFormat.exe” by double-clicking on it.
7. Select “Create File Container”, then “Standard TrueCrypt Volume”
8. Where it says Volume Location, enter “F:secretfile” (substituting the drive letter of your USB key if it is not F.) This is the container in which your encrypted files will be stored.
9. Keep the standard options on the next screen, that of AES and RIPEMD-160.
10. You need to tell the program the size of the encrypted drive you want to create. The container produced will use up that amount of space, so if for instance you created a 100MB encrypted drive, this would take up 100MB of un-encrypted space on your USB key, even if the encrypted area was ’empty’. You may wish to leave room for un-encrypted data. The amount of free space should be displayed to help guide you.
11. Next enter your password, the strength of your password is critical, see below for details on this.
12. Click next and your encrypted drive should now be created, this may take a few minutes depending on the size of your key and speed of your computer.
13. Once complete close the window.
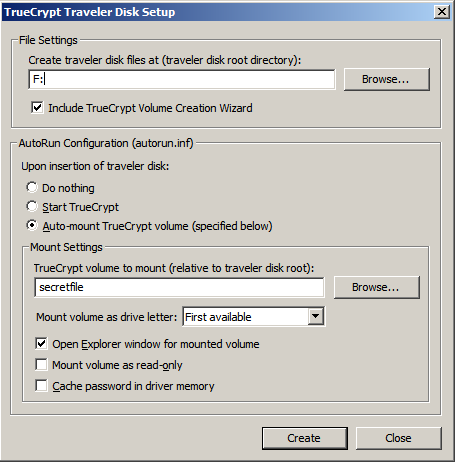
14. Now open the file called “TrueCrypt.exe”, go to the “Tools” option on the menu, then “Traveller Disk Setup”.
15. Under file settings specify the location F:\truecrypt, (changing the drive letter F to whatever the current drive letter is for your USB key). Where it asks for autorun configuration select “Auto-mount”. In the box where it says “file to mount” enter secretfile .
16. Click create, when done, close all windows that you have opened and remove the USB key.
How to use
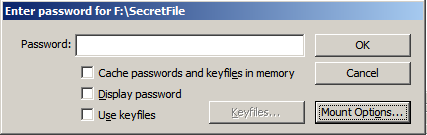
1. Insert USB key. You should get the following popup, select “Mount Truecrypt Volume” and then enter your password at the next prompt. A window should pop up with a new drive letter but there will be no files, yet.
2. To copy files to the new encrypted area just drag and drop as if it was a USB key.
3. To remove the USB key first dismount the key by clicking on the TrueCrypt logo on the right hand side of the status bar and select “Dismount all devices”
What is Encryption?
When you use your password to get into a website it is used to compare it with a list of usernames and paswords to confirm your identity and let you in, that means if you lose your password your supervisor can look it up and remind you of it.
Encryption is different. Think of encryption as your data being scrambled using your password, and not even your supervisor or boss can access it. This means if you lose your password then you can’t get your data back.
How secure is AES-256 Encryption?
It is secure… secure enough for the US government for use with “Top Secret” information. Your encryption, however, is only as strong as your password.
Password Strength
The easiest way to “crack” or hack your encrypted USB key would be to try common passwords or run through the dictionary. The longer and more complicated your password, or pass phrase the safer your data. Try using a password with at least 8 letters, use upper and lower case and numbers. Use more than one word or use a combination of your favourite non-English language words. This is an example of a strong password. “Love”, “Password”, “Arsenal” or your name are all examples of weak passwords.
eg Ouvert1971NerdBoy
Potential Problems
Your local IT department may not allow you to use programmes that run off the USB key because you may not be running as an “administrator”

33 responses so far ↓
1 Nick // Nov 3, 2008 at 1:19 pm
Good review. I’ve gone for the extreme-paranoia approach for my work (windows) laptop, and I’ve encrypted the system drive. It’s pretty reassuring for those “Where’s my laptop?” moments.
By the way – is there a contact email address for this blog? I can’t find one anywhere.
Nick
SpR Respiratory
2 James // Nov 3, 2008 at 7:48 pm
Thanks Nick,
For my Windows XP PC I have also utilised encryption, but with Windows EFS…for “My Documents” the Desktop and temp files…rather than encrypting the whole disk; and with my low-spec PC I did notice a performance hit when I encrypted everything. According to CFH as long as you are using XP-SP1 or above then the encryption will be AES 256.
Presumably you are using TrueCrypt with system disk encryption? If so how did it perform?
Best wishes
James
3 Jay // Jan 7, 2009 at 10:12 am
“Use more than one word […] This is an example of a strong password.”
That is most certainly not true. You should not use combinations of words.
There are about 500.000 words in the English language. Using three words that is binomial(500.000,3) ~ 10^16 possible combinations. Adding 4 numbers in a row gives us around 10^20 possible combinations.
That might sound like much, but is actually well within breaking distance of modern technology.
Using a foreign language improves, but does not solve the problem. A password should not include actual words.
Ouvert1971NerdBoy is not a secure password, sorry.
4 James // Jan 7, 2009 at 1:23 pm
Your point about avoiding using english language and words in a row is good one.
I think though when choosing a password/phrase you need to strike a comprise between something you can remember..(If you have to write it down it sort of defeats the point) and something that is strong enough.
Still with 10^20 combinations, assuming you can try a billion different passwords a second then it would still take 3000 years to crack your key.
5 Brian // Jan 28, 2009 at 6:48 pm
I like when I stumble across something like this on a blog that gives simple directions for something that I have been looking into. Thanks for the blog post, it’s making me lean heavily towards TrueCrypt for ease of usage and the great price, FREE!
6 Carl // Feb 27, 2009 at 8:33 pm
Just what I require. Thank You.
Am I OK to document this article with a link to this site and distribute to my colleagues?
7 James // Feb 27, 2009 at 9:44 pm
Yes, of course.
8 J. // Mar 5, 2009 at 1:15 am
Google “diceware” for help creating strong yet memorable passwords using words.
9 JFtrini // Mar 8, 2009 at 9:28 am
Hi James,
If this method is used to encrypt a usb drive, does it store an executable version of the software on the drive so that it can be opened on any pc?
10 James // Mar 8, 2009 at 10:43 am
Yes…and it will auto-run on most PCs.
11 Dima // Mar 14, 2009 at 1:14 pm
Hi James,
I make all step-by-step, but when I plugin my usb flash disk, I am not get a popup when i must enter my password, it is seems like a autorun not working?
Thnx
12 James // Mar 15, 2009 at 9:30 am
This may be that your version of windows is blocking the auto-insert dialogue.
If you right click on the drive letter in Windows Explorer and click “AutoPlay” it should give you the chance to run TrueCrypt.
13 +chris+ // May 6, 2009 at 2:07 pm
Hi Dima,
Try “15. Under file settings specify the location F: (changing the drive letter F to whatever the current drive letter is for your USB key) ”
instead of
“15. Under file settings specify the location F:\truecrypt”
14 Jaggy // May 11, 2009 at 10:25 am
Hi, I have a USB dongle key. Are you having a program to run my software without the key? Please reply boss. Thanks.
15 keith (GP) // Jun 23, 2009 at 3:32 pm
Great article. In the Irish health service an unencrypted laptop has just been stolen, containing patient details, so this is on everyone’s mind at the moment. K ps what is the reason for transcribibg the characters below, i’ve often wondered
16 James // Jun 23, 2009 at 3:51 pm
The letters below are to check you are a human. Without this test, known as a Captcha, rogue computer programmes known as bots place comments advertising drugs/pornography etc.
Best Wishes
James
17 DaveJ55 // Oct 25, 2009 at 1:26 pm
Safest way with treucrypt is using a password, a key file on your laptop (ans/or desktop) and crypted usb-memkey !! Never lose the key-file or password. No one can acces your files without one of those three !
18 Sandeep // Oct 30, 2009 at 5:57 pm
I apologize for being naive but I encrypted a folder on my machine and I would like to understand that since I can still view the mounted drive and the files within, Will any other user who logs in to my machine be able to view the files in the same way then how can this encryption prevent the files/data to be stolen or in other words how is it safe? Thanks!
19 SecurityGuy // Feb 2, 2010 at 9:57 am
On the subject of secure passwords, one method I’ve found that works for me and doesn’t rely on dictionary words is to pick a long, memorable phrase, then use first characters and other substitutions.
For example: “The quick brown fox jumps over the lazy dog to encrypt his password for truecrypt” becomes “Tqbfjotld2ehp4t”.
Decent length, fairly random, reasonably memorable.
20 dengkos // Mar 2, 2010 at 6:35 am
What if yer “secretfile” corrupted ? And those data inside that container are badly needed. Sure it would be a disaster i supposed.
21 Lumberjack // Mar 10, 2010 at 6:24 pm
1. Regarding the corruption of the truecrypt container, take a lesson from Chicago and Louisiana politics: backup early and often.
2. Truecrypt’s problem on USB drives is that it will only work on computers on which you have Administrator priviledges. Try SanDisk drives with U3 software.
22 Ozena // Mar 23, 2010 at 3:04 pm
One more free encryption software that doesn’t require admin rights on a guest computer is Rohos Mini Drive – easy and slick.
23 Nick // Mar 29, 2010 at 6:14 pm
Still using system encryption on XP SP3 TrueCrypt on the work laptop 17 months after http://www.medicalnerds.com/encrypting-a-usb-key-using-truecrypt/#comment-5842 … irritated by my hospital’s insistence on using proprietary encryption systems for USB drives for which will have a) cost more and b) be less secure than TrueCrypt.
24 Marc // May 23, 2010 at 9:40 pm
Thanks for the info – I’m not in the medical field, but I still needed a solution like this to encrypt private data for a colleague’s USB drive.
He’s not so tech savvy, so I was sure to select the “Auto-mount” option so it won’t be too painful or confusing for him to use.
Cheers!
25 steve // Aug 8, 2010 at 8:12 am
People always complain about strong passphrases being difficult to remember but that just suggests a bad strategy for picking a passphrase.
Heres an example strategy:
– pick a base passphrase which will be used for all passwords. To do this, think of a phrase, quote or line from a song. Im going to choose “To be or not to be, that is the question” from “Hamlet”. Take the initial letters and you’re left with a seemingly random string of characters (tbontbtitq). Captilize the last letter and substitute words for numbers and you have “2bon2btitQ”.
– For each website you register on, take the nth (lets say 1st) letter of their domain. Put this letter capitilized at a designated position (lets say 3rd) in the base passphrase… now we have 2bEon2btitQ for ebay, 2bAon2btitQ for amazon. Now you have 26 unique passwords. If your ebay password is compromised, your paypal password will still be secured.
That might seem like alot to remember, but you’d be suprised how easy it is to remember once you commit to it. I’d suggest doing it for one website to begin with, then look to do it for the others.
26 Pierre // Aug 19, 2010 at 3:20 pm
What if someone erase the TrueCrypt files, I lose all my protected data?
27 James Porter // Oct 6, 2010 at 7:02 pm
Nice article however how are you going to make TrueCrypt prompt you for username and password once inserted? you need to create an autorun.inf, otherwise it is going to be a little hard to use. There is a really good article in GeekyProjects, that talks about this.
http://geekyprojects.com/usb-encryption/how-to-encrypt-usb-flash-drives-using-truecrypt/
28 john moore // Oct 11, 2010 at 9:14 am
I have to change my password at work every 3 months. I use patterns on the keyboard like qaz741 . After a while you run out of good pass words.
29 littlebearz // Mar 13, 2011 at 1:12 am
lmao i use GPG to encrypt my stuff, usually i do base, which is the everyday password that we use, and add my cat name in additional to the date last modified, the only problem is that if someone renamed the file, I’m screwed as i need to know the date in order to recover my data lol.
30 tsugaman // Nov 7, 2011 at 4:54 am
I’m sorry but I’m obviously missing something that all of you can understand (that is if you followed these directions).
I followed the directions to the letter and went over it twice and everything works until you get to #15. When I enter I:truecrypt (“I” is the letter of my drive) in traveller root directory I get the error “System cannot find the path specified”. I checked the drive and all it has is in it is secretfile, no truecrypt or truecrypt.exe or anything.
I tried copying all the extracted files including the “sys” files to the drive and still get the error. When you click the browse button all you can do is direct it to the “root directory” which is I:\
Do I have to mount the secret file before this will work? Are you using an older version of Truecrypt? Either must be missing something that everyone else can see without question because no one else has brought this up.
31 tsugaman // Nov 7, 2011 at 5:05 am
“When I enter I:truecrypt (”I” is the letter of my” should of read works until you get to #15. When I enter I:\truecrypt (”I” is the letter of my.
forgot to the backslash in the sentence.
Note: also tried with capitol T and C as name of TrueCrypt.exe is written.
32 tsugaman // Nov 7, 2011 at 8:55 am
One more note (I hope someone can help with this): I tried step 15 with just L:\ and it creates it fine but when I put the USB drive in the only thing that gets automounted is the drive itself. So a folder opens showing the contents of the drive instead Truecrypt starting and asking for a password.
Thanks somene.
33 Yo // Jan 18, 2012 at 8:54 am
I have followed steps 1-12 for a 8GB USB drive (NTFS formatted) but after the lengthy step 12, I get a series of error messages e.g. ‘Can’t find folder’ ‘can’t mount…’ ‘aborted…’
Any idea what I’m doing wrong?
Leave a Comment
(Don't forget to fill in the Captcha)